Projects
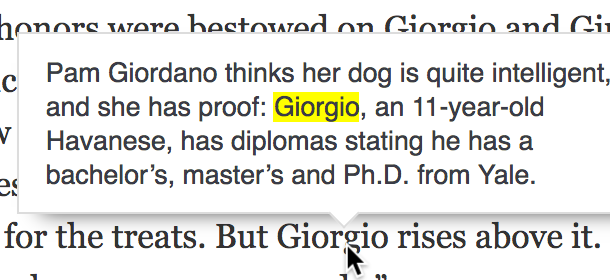 First Mention, a browser extension to remind you who people are who were introduced earlier in an article
First Mention, a browser extension to remind you who people are who were introduced earlier in an article
 New York Times Byline Restorer, a browser extension that restores bylines and removes “x min read” lines on the NYT homepage
New York Times Byline Restorer, a browser extension that restores bylines and removes “x min read” lines on the NYT homepage
Posts
November 2015
Automated Scanning of Firefox Extensions is Security Theater (And Here’s Code to Prove It)